




























 Image: Getty/Bloom Productions
Image: Getty/Bloom Productions Keeping on top of cybersecurity risks is a constant challenge. Threats including phishing, malware and ransomware are continually evolving and adapting, as cyber criminals regularly find new, innovative ways to conduct malicious hacking campaigns, break into computer systems and find a way to stay there.
Security threats like malware, ransomware and hacking gangs are always evolving. This special report explains what you need to focus on next.
Read nowThis combination is proving difficult for many companies to keep up with, resulting in security holes in networks and vulnerabilities left unpatched. These flaws are relatively simple elements of cybersecurity to manage, but ones with which many organisations are still attempting to grapple.
Even more bad news: the way in which cybersecurity and cybersecurity threats keep evolving means there's the risk that many businesses could be left behind and dangerously exposed as technology moves forward -- and cyber threats move forward with it.
Quantum computing is increasingly gaining traction, with big tech companies setting out plans to deliver high-powered quantum computing hardware in the next few years. The power of quantum computing could provide benefits for society in several ways, particularly when it comes to science, research, analyising algorithms, as well as improving artificial intelligence and machine learning.
But there's the risk that the rise of quantum computing poses a threat to traditional cybersecurity and encryption as we know it because quantum computers could break public-key cryptography -- it's something the White House has warned could be a threat to businesses and national security.
For now, the encryption used to protect data is strong enough, at least when it comes to protecting it from traditional computers. The problem is that with the arrival of quantum computing, those cryptography protocols that date back decades could be challenged by high-performance quantum machines.
It's also easy to imagine nation state-backed hacking groups trying to exploit quantum computing to commit cyber espionage (or to decode encrypted data they have stolen in the past). It's even possible that cyber-criminal groups will also look to exploit quantum to help increase the efficiency of financially motivated cyberattacks.
That threat could come in the form of using quantum computing to breach passwords and other cybersecurity defences to enter the network and install ransomware or other malware. Or attackers could deploy quantum-strengthened encryption to encrypt files as part of ransomware attacks, which are impossible to break or reverse using classical computers, meaning that a victim has no choice but to pay a ransom for a decryption key.
Technology companies are working on quantum-proof cybersecurity -- and it's likely to be something that many governments, businesses and other organisations will need to think about in the coming years.
The world has already seen how disruptive a cyberattack against a major software supplier can be. The attack on SolarWinds by, what was later revealed to be the Russian foreign intelligence service, saw hackers infiltrating the software-building process and infecting legitimate software updates with malware.
Unfortunately, this is likely just a taste of what's to come, especially as more and more organisations turn towards software as a service and cloud-based technological solutions.
Your own network could be as resilient as possible to cyberattacks, but if one of your suppliers gets their network cracked by hackers, they then have an easy way into the network.
Concepts like 'secure by design' can help improve cybersecurity for everyone, but with IT and cybersecurity budgets already facing challenges and software companies making tempting targets for cyber criminals, it's unlikely that software supply chain attacks will become a thing of the past any time soon.
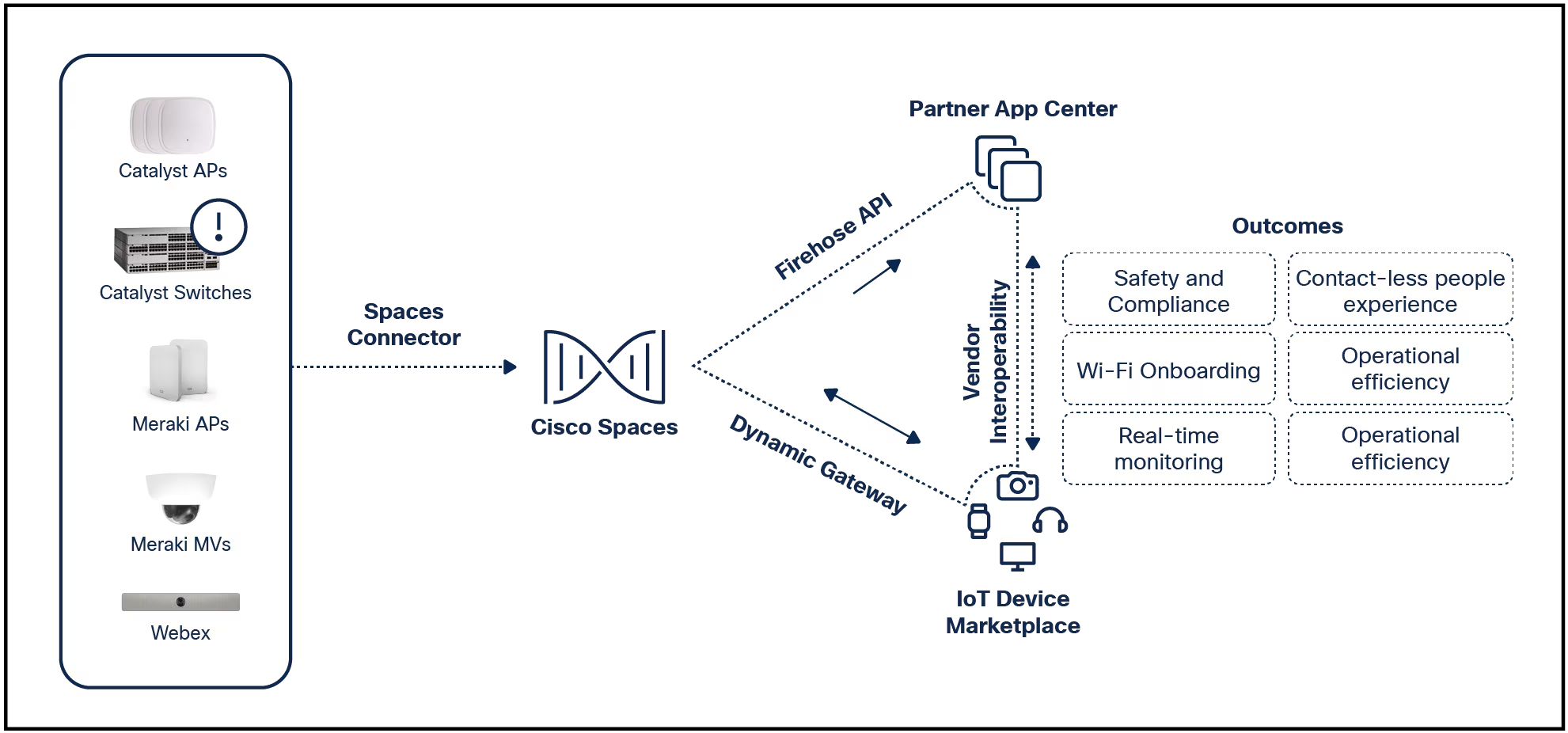
Many different industries are increasingly rolling out Internet of Things (IoT) connected devices. From huge factories connecting IoT devices to production lines to monitor wear and tear, hospitals using wearable technology to treat and monitor patients to smart meters and other smart devices increasingly used in the home, more and more IoT products are being connected to networks.
While they're being adopted because they provide benefits and services to users, they also risk making users more vulnerable to cyberattacks because many IoT devices are inherently insecure.
Cyber criminals can search for IoT devices facing the public internet and can exploit the lack of security controls in many devices to gain access to networks. In one example, hackers accessed an internet-connected fish tank at a casino and used it as an entry point to steal information about customers.
While some steps are being taken to improve IoT security, they're currently very limited, particularly as manufacturers continue to rush products out to the marketplace, seemingly without giving much thought to cybersecurity. Cyber criminals know IoT is an easy target and the problem is likely to get worse before it gets better.
Business email compromise (BEC) attacks are already one of the most successful forms of cyber crime -- according to the FBI, it costs companies billions every single year.
The most common way BEC attacks are carried out is via email, with cyber criminals hacking into legitimate email accounts belonging to bosses and requesting staff make large financial transactions. One of the ways victims are tricked into this attack is that they're told they are working on a secret business deal that needs to be done very quickly.
But the money isn't being transferred to another business -- instead, it's being transferred to a bank account operated by the cyber criminals. The transactions often amount to hundreds of thousands of dollars and, by the time anyone notices something is wrong, the fraudsters have taken the money.
BEC attacks are already highly successful using email. The emergence of deepfakes and other technologies could make the situation much worse.
While people might be more suspicious of an email claiming to be from their boss, they could be more easily convinced to make the transfer if they think they're face to face with the real person, with the attacker using technology to look and sound like their CEO.
The FBI has warned that cyber criminals are already using deepfakes to apply for remote jobs and deepfake technology is only going to get better as we move forward, making it more difficult to tell the difference between videos of real people and videos of people generated by artificial intelligence and machine learning.
But as demonstrated by countless cyber incidents, malware and cyberattacks powered by traditional computing power can still cause plenty of damage and disruption.
Malware has been used to shut down nuclear plants and power stations. Global events, such as the WannaCry ransomware attack and the NotPetya attack, demonstrated how disruptive cyberattacks can be.
NotPetya was particularly disruptive, causing hundreds of billions in damages around the world. Western governments blamed the attack on Russia, which launched the campaign against businesses in Ukraine -- but the interconnected nature of global computer systems meant that the attack spread across much of the world.
Russia has never accepted responsibility for NotPetya, or a string of destructive wiper malware attacks launched against Ukraine in the run up to and during Russia's invasion of the country.
While these wiper campaigns have mostly focused on Ukraine, there's the possibility that a rogue state could look to launch similar destructive attacks around the world. It's another cybersecurity risk that businesses should think about planning resilience strategies around.
One threat that is here already -- and only likely to get worse -- is the lack of trained staff to fill the vast numbers of empty tech security roles. Having the security team in place to build the defences and make sure they are maintained continues to be a problem for companies big and small and will magnify the risks created by all the other new threats.
While preparing for the cybersecurity threats of the future is a must, it can't be done without taking care of the cybersecurity that we're faced with at present. Being on top of cybersecurity and as protected as you can be against cyberattacks today can provide a major step towards preparing to protect against the cyberattacks of tomorrow.
 Tags quentes :
Tecnologia
Segurança
Tags quentes :
Tecnologia
Segurança