






























 Cyble
Cyble A new Remote Access Trojan (RAT) might have an amusing name to some, but its capabilities show the malware to be no laughing matter.
While robust passwords help you secure your valuable online accounts, hardware-based two-factor authentication takes that security to the next level.
Read nowDubbed Borat RAT, Cyble Research Labs said in a recent malware analysis that the new threat doesn't settle for standard remote access capabilities; instead, Borat RAT also includes spyware and ransomware functions.
According to the cybersecurity researchers, the Trojan, named after the character adopted by comedian Sacha Baron Cohen, is offered for sale to cybercriminals in underground forums.
Borat RAT has a centralized dashboard and is packaged up with a builder, feature modules, and a server certificate.
The malware's capabilities are vast and include a keylogger, a ransomware encryption and decryption component -- as well as the option for users to generate their own ransom notes -- and an optionally distributed denial-of-service (DDoS) feature for "disrupting the normal traffic of a targeted server," according to Cyble.
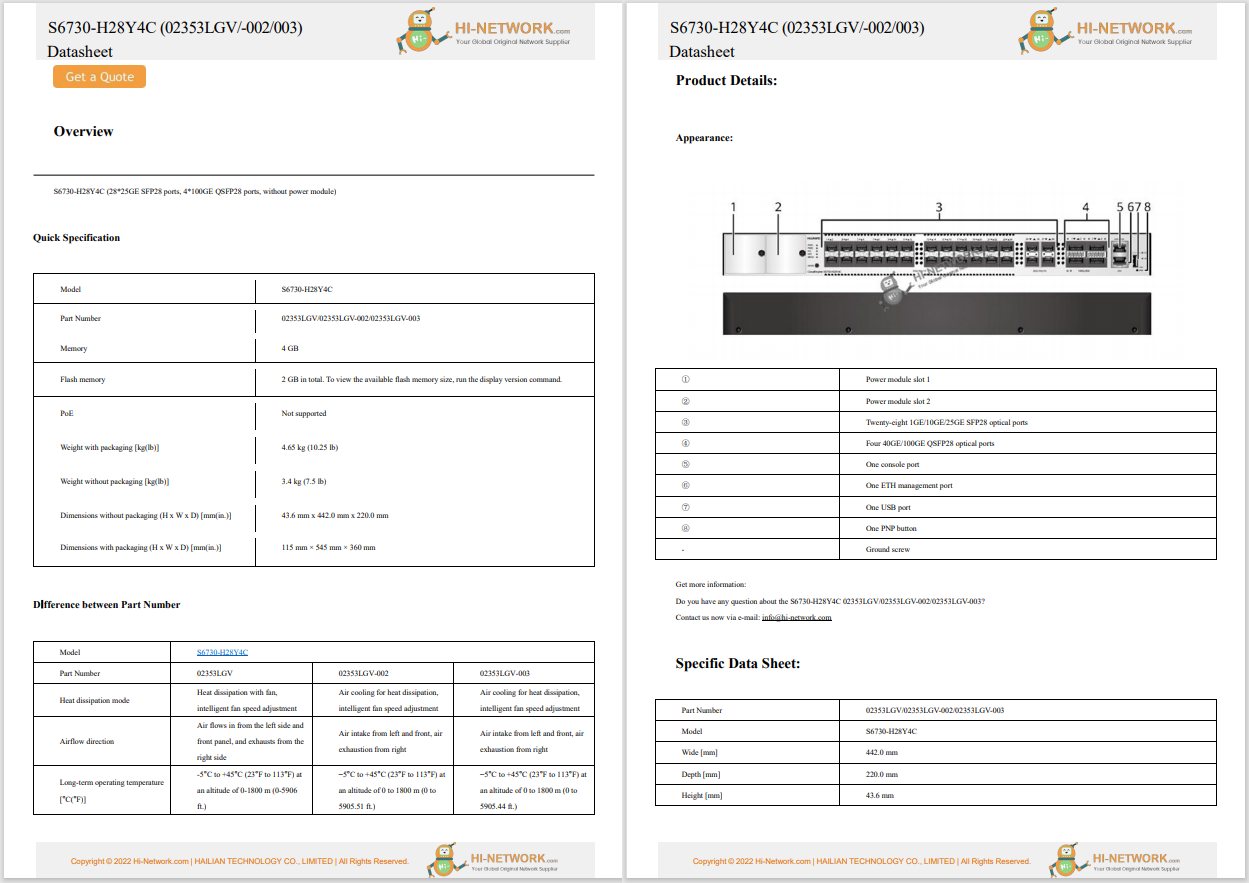
Some of Borat RAT's marketed capabilities
CybleThe use of 'RAT' in the name is a clue to the remote and surveillance features of the malicious software. Borat RAT can remotely record a machine's audio by compromising its microphone, capture webcam footage and also contains a host of remote control options: hijacking a mouse or keyboard, performing screen captures, tamping with system settings, and both stealing and deleting files.
Borat RAT utilizes process hollowing for compromising legitimate processes on a target machine and may also enable reverse proxies to stay under the radar when performing malicious activities.
The malware will harvest data, including operating system information, before sending it to an attacker-controlled command-and-control (C2) server. Furthermore, Borat RAT will hone in on browser information such as cookies, browser histories, bookmarks and favorites, and account credentials.
Browsers such as Chrome and Chromium-based Microsoft Edge are impacted. Discord tokens, too, can be stolen.
Cyble says that the malware can also perform other functions to "disturb" its victims, including playing audio, swapping mouse buttons, showing or hiding a desktop and taskbar, freezing the mouse, tampering with webcam lights, turning off a monitor, and more.
Despite its name, remote control, spyware, and ransomware capabilities make Borat RAT a potent malware strain worth watching. Cyble intends to monitor the development of the "unique" malware in the future.
See also
Have a tip?Get in touch securely via WhatsApp Signal at +447713 025 499, or over at Keybase: charlie0
 Tags quentes :
Tecnologia
Segurança
Tags quentes :
Tecnologia
Segurança