




























Coding errors in software products provide easy paths of entry for online criminals, who can exploit vulnerabilities to compromise systems or launch additional attacks and malware. As reported in theCisco 2015 Midyear Security Report, certain types of coding errors consistently appear on lists of most common vulnerabilities. This raises an important question for vendors and security professionals: If the same coding errors are identified year in and year out, why aren't these errors being mitigated?
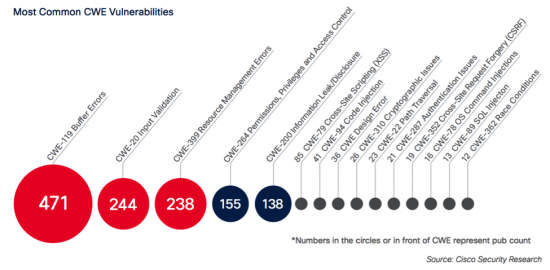
Buffer errors, input validation, and resource errors are usually among the most common coding errors exploited by criminals, according to the list of Common Weakness Enumeration (CWE) threat categories. As we explain in theMidyear Security Report, the likely culprit is the lack of sufficient attention paid to security during the product development lifecycle. In many cases, vendors wait until products come to market, and only then resolve vulnerabilities. However, this process should be reversed. Vendors should build security safeguards and conduct vulnerability testing during product development, in order to lessen the chance that criminals can profit -and customers can suffer.
To reduce the occurrence of these common code errors, software developers should participate in regular security training to build awareness of current vulnerabilities, trends, and threats. In addition, organizations should add security checkpoints and reviews throughout the development lifecycle to detect and correct vulnerabilities as early as possible. Security code reviews should be completed by a dedicated team outside of product development, in order to provide unbiased reviews and recommendations.
Executive support should play a key role in secure development. Development life cycle policies and procedures should require executive signoff to accept risk, require development projects to correct security issues before moving forward, or stop a product or software deployment until security reviews and corrections are completed.
TheChallenge of Open-Source Vulnerabilities
As open-source solutions become more popular, they require extra vigilance from security professionals. As Cisco details in theMidyear Security Report, closing up vulnerabilities in open-source solutions requires extra coordination. Developers may be able to come up with a quick patch, but vendors then need to add these fixes to the many versions of their products that rely on the open-source solutions. To help security professionals better understand how open-source solutions are used in their organizations, they must also rely more heavily on software supply chain management. The most common vulnerabilities tracked by Cisco in 2015 are shown below.

The good news is that there are movements afoot to respond quickly to vulnerabilities in open-source products. When security researchers detected the VENOM (Virtualized Environment Neglected Operations Manipulation) vulnerability, which affected open-source code for virtualization systems, vendors released patches even before the vulnerability was announced.
In addition, several leading technology companies, including Cisco, are donating to the Linux Foundation to help improve OpenSSL infrastructure. These donations will help security researchers review open-source code and identify appropriate fixes and patches.
Projects that use open-source code should apply the same rigorous security testing and reviews that developers provide for non-open source projects, as a way to contribute back to the security of open-source. Also, vendors should document where and how open-source code is used in their solutions, which will help speed response time when vulnerabilities and threats are uncovered.
Slight Increase in IntelliShield Alert Totals
The Cisco 2015 Midyear Security Reportalso includes updates on alerts and vulnerabilities tracked by Cisco researchers. Cumulative annual alert totals for the first five months of 2015 have risen slightly compared to the same period in 2014. The likely cause of the increase is greater vendor focus on security testing, as well on identifying vulnerabilities.
The growing volume of vulnerabilities being identified and corrected requires more efficient vulnerability management processes. To keep up with vulnerabilities, organizations should automate management for inventories, data correlation, basic analysis and triage.
To support secure development lifecycle and vulnerability management, vendors like Cisco-as well as security organizations such as the Industry Consortium for Advancement of Security on the Internet (ICASI), the National Council of ISACs, and the U.S. Department of Homeland Security-are working to improve vulnerability information sharing and reporting in standardized formats. Organizations can find additional guidance on the various security frameworks through documents from The Open Group's Architecture Maturity Models, and documents from the U.S. National Institute of Standards and Technology.
To learn more, download theCisco 2015 Midyear Security Report.
 Tags quentes :
Segurança
Código aberto
Cisco Midyear Security Report
2015 midyear security report
MSR
Tags quentes :
Segurança
Código aberto
Cisco Midyear Security Report
2015 midyear security report
MSR