




























During our threat hunting exercises in recent months,we've started to observe a distinguishing pattern ofmsiexec.exeusage across different endpoints. As we drilled down to individual assets,we found traces of a recently discovered malware called Raspberry Robin. The RedCanary Research Team first coined the name for this malware in their blog post,and Sekoia published a Flash Report about the activity under the name of QNAP Worm. Both articles offer great analysis of the malware's behavior. Our findings supportandenrich prior research on the topic.
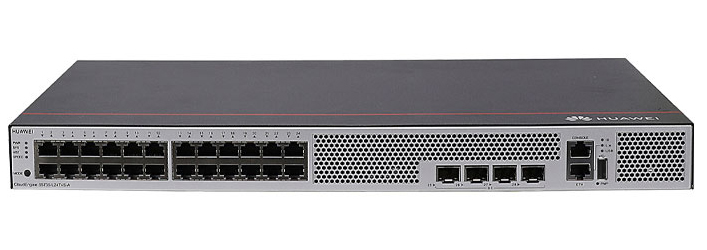
Raspberry Robin is a worm that spreads over an external drive. After initial infection,it downloads its payload throughmsiexec.exefrom QNAP cloud accounts, executes its code throughrundll32.exe,and establishes a command and control (C2) channel through TOR connections.
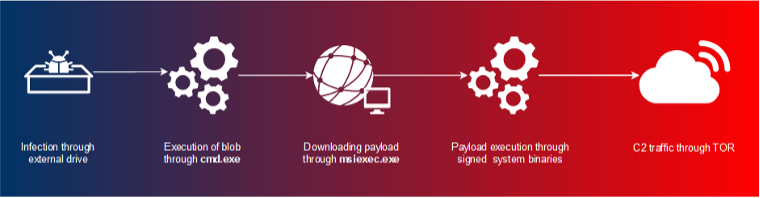 Image 1: Execution chain of Raspberry Robin
Image 1: Execution chain of Raspberry RobinLet's walkthrough the steps of the kill-chain to see how this malware functions.
Raspberry Robin is delivered through infected external disks. Once attached,cmd.exetries to execute commands from a file within that disk. This file is either a.lnkfileora file with a specific naming pattern. Files with this pattern exhibit a 2 to 5 character name with an usually obscure extension, including.swy, .chk, .ico, .usb, .xml,and .cfg.Also, the attacker uses an excessive amount of whitespace/non printable characters and changing letter case to avoid string matching detection techniques. Example command lines include:
File sample for delivery can be found in this URL:
https://www.virustotal.com/gui/file/04c13e8b168b6f313745be4034db92bf725d47091a6985de9682b21588b8bcae/relations
Next, we observeexplorer.exerunning with an obscure command line argument, spawned by a previous instance ofcmd.exe. This obscure argument seems to take the name of an infected external drive or.lnkfile that was previously executed. Some of the samples had values including USB, USB DISK, or USB Drive, while some other samples had more specific names. On every instance ofexplorer.exewe see that the adversary is changing the letter case to avoid detection:
After delivery and initialexecution, cmd.exespawnsmsiexec.exeto download the Raspberry Robin payload. It uses-q or /qtogether with standard installation parameter to operate quietly. Once again, mixed case letters are used to bypass detection:
As you can see above, URLs used for payload download have a specific pattern. Domains use 2 to 4 character names with obscure TLDs including.xyz, .hk, .info, .pw, .cx, .me,and more. URL paths have a single directory with a random string 11 characters long, followed by hostname and the username of the victim. On network telemetry, we also observed theWindows Installeruser agent due to the usage ofmsiexec.exe. To detect Raspberry Robin through its URL pattern, use this regex:
^http[s]{0,1}\:\/\/[a-zA-Z0-9]{2,4}\.[a-zA-Z0-9]{2,6}\:8080\/[a-zA-Z0-9]+\/.*?(?:-|^http[s]{0,1}\:\/\/[a-zA-Z0-9]{2,4}\.[a-zA-Z0-9]{2,6}\:8080\/[a-zA-Z0-9]+\/.*?(?:-|\=|\?).*?|\?).*?$
If we look up the WHOIS information for given domains, we see domain registration dates going as far back as February 2015. We also see an increase on registered domains starting from September 2021, which aligns with initial observations of Raspberry Robin by our peers.
| WHOIS Creation Date | Count |
| 12/9/2015 | 1 |
| ... | ... |
| 10/8/2020 | 1 |
| 11/14/2020 | 1 |
| 7/3/2021 | 1 |
| 7/26/2021 | 2 |
| 9/11/2021 | 2 |
| 9/23/2021 | 9 |
| 9/24/2021 | 6 |
| 9/26/2021 | 4 |
| 9/27/2021 | 2 |
| 11/9/2021 | 3 |
| 11/10/2021 | 1 |
| 11/18/2021 | 2 |
| 11/21/2021 | 3 |
| 12/11/2021 | 7 |
| 12/31/2021 | 7 |
| 1/17/2022 | 6 |
| 1/30/2022 | 11 |
| 1/31/2022 | 3 |
| 4/17/2022 | 5 |
Table 1: Distribution of domain creation dates over time
Associated domains have SSL certificates with the subject alternative name of q74243532.myqnapcloud.com, which points out the underlying QNAP cloud infra. Also, their URL scan results return login pages to QTS service of QNAP:
 Image 2: QNAP QTS login page from associated domains
Image 2: QNAP QTS login page from associated domainsOnce the payload is downloaded, it is executed through various system binaries. First,rundll32.exeuses theShellExec_RunDLLfunction fromshell32.dllto leverage system binaries such asmsiexec.exe, odbcconf.exe, orcontrol.exe.These binaries are used to execute the payload stored in C:\ProgramData\[3 chars]\
It is followed by the execution offodhelper.exe, which has the auto elevated bit set to true. It is often leveraged by adversaries in order to bypass User Account Control and execute additional commands with escalated privileges[3]. To monitor suspicious executions offodhelper.exe,we suggest monitoring its instances without any command line arguments.
Raspberry Robin sets up its C2 channel through the additional execution of system binaries without any command line argument, which is quite unusual. That likely points to process injection given elevated privileges in previous steps of execution. It usesdllhost.exe, rundll32.exe, and regsvr32.exeto set up a TOR connection.
In Cisco Global Threat Alerts available through Cisco Secure Network Analytics and Cisco Secure Endpoint, we track this activity under the Raspberry Robin threat object. Image 3 shows a detection sample of Raspberry Robin:
 Image 3: Raspberry Robin detection sample in Cisco Global Threat Alerts
Image 3: Raspberry Robin detection sample in Cisco Global Threat AlertsRaspberry Robin tries to remain undetected through its use of system binaries, mixed letter case, TOR-based C2, and abuse of compromised QNAP accounts. Although we have similar intelligence gaps (how it infects external disks, what are its actions on objective) like our peers, we are continuously observing its activities.
| Type | Stage | IOC |
| Domain | Payload Delivery | k6j[.]pw |
| Domain | Payload Delivery | kjaj[.]top |
| Domain | Payload Delivery | v0[.]cx |
| Domain | Payload Delivery | zk4[.]me |
| Domain | Payload Delivery | zk5[.]co |
| Domain | Payload Delivery | 0dz[.]me |
| Domain | Payload Delivery | 0e[.]si |
| Domain | Payload Delivery | 5qw[.]pw |
| Domain | Payload Delivery | 6w[.]re |
| Domain | Payload Delivery | 6xj[.]xyz |
| Domain | Payload Delivery | aij[.]hk |
| Domain | Payload Delivery | b9[.]pm |
| Domain | Payload Delivery | glnj[.]nl |
| Domain | Payload Delivery | j4r[.]xyz |
| Domain | Payload Delivery | j68[.]info |
| Domain | Payload Delivery | j8[.]si |
| Domain | Payload Delivery | jjl[.]one |
| Domain | Payload Delivery | jzm[.]pw |
| Domain | Payload Delivery | k6c[.]org |
| Domain | Payload Delivery | kj1[.]xyz |
| Domain | Payload Delivery | kr4[.]xyz |
| Domain | Payload Delivery | l9b[.]org |
| Domain | Payload Delivery | lwip[.]re |
| Domain | Payload Delivery | mzjc[.]is |
| Domain | Payload Delivery | nt3[.]xyz |
| Domain | Payload Delivery | qmpo[.]art |
| Domain | Payload Delivery | tiua[.]uk |
| Domain | Payload Delivery | vn6[.]co |
| Domain | Payload Delivery | z7s[.]org |
| Domain | Payload Delivery | k5x[.]xyz |
| Domain | Payload Delivery | 6Y[.]rE |
| Domain | Payload Delivery | doem[.]Re |
| Domain | Payload Delivery | bpyo[.]IN |
| Domain | Payload Delivery | l5k[.]xYZ |
| Domain | Payload Delivery | uQW[.]fUTbOL |
| Domain | Payload Delivery | t7[.]Nz |
| Domain | Payload Delivery | 0t[.]yT |
 Tags quentes :
Cognitive Intelligence
msiexec
qnap worm
raspberry robin
Tags quentes :
Cognitive Intelligence
msiexec
qnap worm
raspberry robin