




























Cisco Security helped secure the Black Hat Europe 2018 Network Operations Centre (NOC) for the second year; joining conference producer UBM and its other security partners RSA Security, Palo Alto Networks, Rukus and Gigamon. Cisco provided DNS visibility and threat intelligence with Cisco Umbrella and Cisco Investigate; and automated malware analysis and threat intelligence with Cisco Threat Grid, backed by Cisco Talos Intelligence and Cisco Threat Response.
Like other Black Hat conferences, the mission of the NOC is to build the conference network that is secure, stable and accessible for the training events, briefings, sponsors and attendees. This requires a robust connection to the Internet (Gigamon), firewall protection (Palo Alto Networks), segmented wireless network (Rukus) and network full packet capture and forensics (RSA NetWitness); with Cisco providing cloud-based security and intelligence support. The trainers, briefers and sponsors need to be able to access and demonstrate malicious code and network activity; without infecting attendees or other networks, or experiencing an outage. It is a balancing act that the NOC team enjoys helping perform at each conference.
Black Hat Europe 2018 activity in the NOC was exciting from the first day and it never let up through the week. NOC leaders @grifter and @thestump3r give an out briefing at the end of each conference, on some of the highlights of the security incidents and network metrics; and the security partners each have the ability to blog about some of their findings.
Variants of Obfuscated Malware
As the network packets flowed, our partner RSA NetWitness inspected them for potential threats, including misnamed files. During the training portion of the conference, a file called table.png was downloaded. NetWitness identified the file header as MZ, which is an executable, and submitted it to Threat Grid for dynamic analysis.

Within minutes of submission, table.png was identified as the Trickbot trojan, along with two additional variants (unique hash values), also submitted by NetWitness to Threat Grid.

Trickbot was identified by Threat Grid because of the mutex, where it is using the same process space in memory as other Trickbot versions. It is very easy to change a hash value, by flipping one bit; however, it is much more work to rewrite your code's use of memory.

Trickbot is a banking trojan which appeared in late 2016. Due to the similarities between Trickbot and Dyre; it is suspected some of the individuals responsible for Dyre are now responsible for Trickbot. Trickbot has been rapidly evolving over the months since it has appeared; however, Trickbot is still missing some of the capabilities Dyre possessed. Its current modules include DLL injection, system information gathering and email searching.
The RSA team investigated the MAC address of the user downloading the Trojan masquerading as a .png file. Starting from the beginning of all activity from this device, within minutes of joining the network there were hundreds of dynamic domain generation algorithm beacons, malware downloads from a Macintosh laptop. Most likely someone with a lab VM (Windows) was testing/demoing/scripting malware execution. The NOC team took steps to ensure the malware stayed confined to that user.
Intelligent Proxy
On the first day of the trainings, we enabled the Intelligent Proxy on Umbrella, to gain visibility into threats, content or apps; by proxying web connections for risky domains. That morning, there was a malware activity alert for an DNS request for macautofixer. With the Intelligent Proxy, we were able to see the file downloaded.

There was an investigation by the NOC team, including firewall logs and network packet reconstruction, and which user's machine made the request.
We provided additional global threat intelligent visibility with Investigate.

Including the distribution of the DNS requests by geography.

The NOC team identified the infected machine as an asset of a conference staff member and took remediation steps. The standard at Black Hat is to allow DNS traffic, including that which is malicious, until we identify an external attack such as this. In this case, that domain was blocked in Umbrella for this and all future Black Hat conferences.
On the second day of training, the firewall team noticed a few users on the Black Hat Wi-Fi were infected with Simba, attempting communication with the old command and control domain.
www[.]gadyniw[.]com/hbt.php?rewrite=login.php
purycap[.]com/login.php
gadyniw[.]com/hbt.php?rewrite=login.php
ww1[.]ysyfyj[.]com/login.php
The gadyniw domain traffic, detected with Threat Grid intelligence integration to Cisco Umbrella, would have been blocked by default as malicous.

The incident was investigated by the NetWitness team, who replayed the sessions. The NOC team verified it was class material; and we requested the instructor ask his students to stay in the class Wi-Fi and not go to the public access segment.
Distribution of Global requests for gadyniw and identification of associated Trojan with Threat Grid integration.

Phishing Attack
During the conference, the staff at UBM were subjected to a coordinated phishing campaign via email, which remains the most common vector for attack.

We investigated the link in the 'CLICK HERE' within the body of the email, using the Glovebox feature of Threat Grid to interact with the virtual machine, without the risk of infection. In two browsers, the link returned an error page.

However, looking at the activity in the analysis report, there were nearly 100 network streams opened, about 100 artifacts downloaded to disk, including dozens of javascript files, with over 170 changes to the registry.

We added the domain to the block list in Umbrella for all Black Hat conferences, to protect the UBM staff, while still allowing the other "Malicious" DNS traffic to occur for training and demonstration purposes.

DNS Activity
In 2017, there were about 5.8 million DNS requests on the Black Hat Europe network. This year, there were over 7.6 million 2018 requests, of which ~4,000 would have been blocked by default as Malware, Command and Control or Phishing.

New to Black Hat Europe were captured webpage notifications to conference users whose email credentials were passed in plain text, as identified by NetWitness, advising them on steps to secure their email. Thankfully, only 14 users had such misconfigured email clients or servers, a drastic drop from prior conferences. This was the first conference in the last two years, where we did not see financial or banking documents sent by email or downloaded in the clear. Perhaps the new EU privacy law is working?
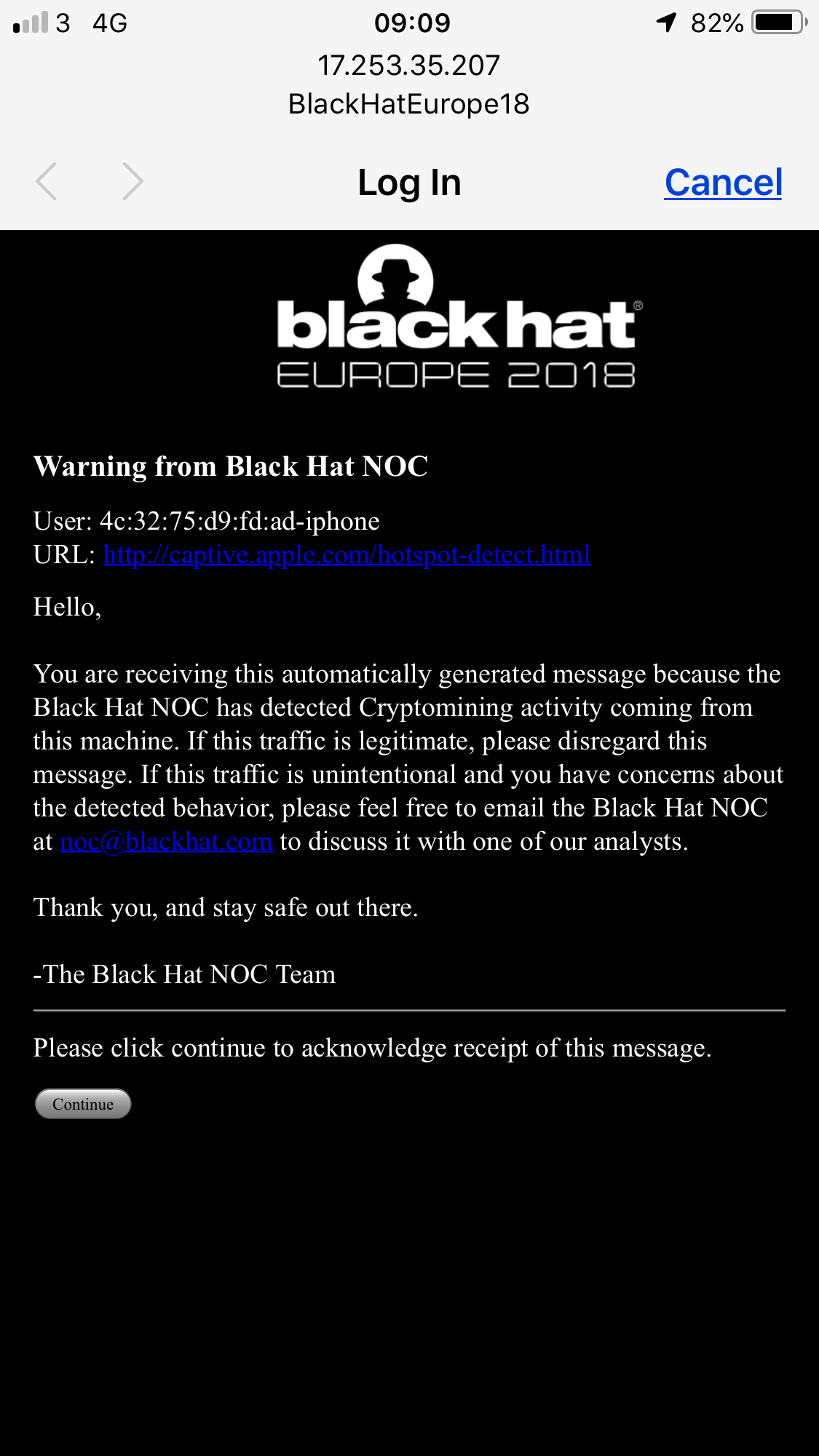
The NOC team also is now alerting users whose devices are seen communicating with cryptomining domains. Black Hat Europe 2017 was the first time we saw cryptomining on the network, with a massive rise at Black Hat Asia 2017.

Possibly infected users were provided a warning, using the NetWitness Orchestrator. If they were using their device to mine cryptocurrency, then carryon. If it was without their consent, the NOC offered their support to remediate.
Also new for this conference was App Discovery, or visibility into the over 2,000 applications used to request DNS.

In a production environment, those applications could have been controlled, such as these Anonymizer Apps, listed in order of most requests.

See you in 2019!
Next stop for the RSA Security and Cisco Security teams is the RSA Conference Security Operations Center; and the Black Hat NOC team will reunited for Black Hat Asia.

Acknowledgements: Special thanks to our NOC partners, especially the RSA Security team and the UBM staff. Also, to Fernando Ferrari, Consulting Security Engineer, Cisco Cloud Security.
 Tags quentes :
Cisco Talos
Cisco Umbrella
Cisco Threat Response
Csco Umbrella Investigate
Cisco Threat Grid
Black Hat Europe
Tags quentes :
Cisco Talos
Cisco Umbrella
Cisco Threat Response
Csco Umbrella Investigate
Cisco Threat Grid
Black Hat Europe